IDP is an anti-virus program for persons who utilize a variety of anti-virus applications.
Generic is a popular moniker for a threat.
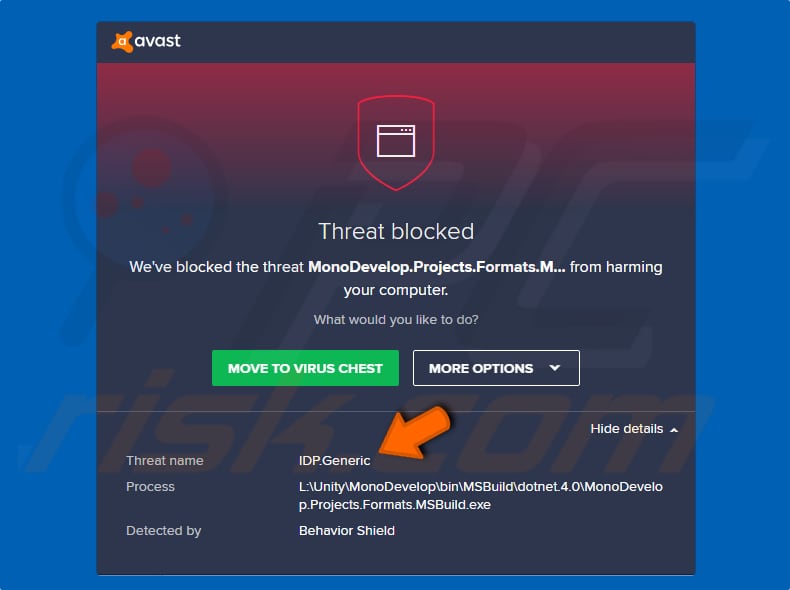
When a security program detects a threat with the name IDP.Generic, it means that it was discovered by this component (Identity Protection), which generalized a detected file.
This detection is often a ‘false positive’.
There are a variety of diseases that could be classified as IDP.Generic dangers.
Take, for instance, a game file.
It is extremely likely that the game will not be able to start if the installed anti-virus software detects it as a danger.
Other programs that include files designated as IDP.Generic threats are also affected.
As previously stated, this threat is classified as a false positive detection. It means that the installed anti-virus program mistook a harmless/legitimate file for a threat and quarantined or deleted it.
These detections can result in the deletion of crucial system files or other important data. However not all detected threats are false positives.
Cyber fraudsters frequently disguise malicious files as genuine files.
They give their files names that are remarkably similar to real files, so they aren’t recognized as threats or harmful.
In this scenario, we recommend that you double-check and run a virus scan with a different application. Make sure your anti-virus (or anti-spyware) software is up to date as well.
If it isn’t, update it and rerun the scan. Check to see if it still detects files as the IDP.Generic threat, and if other security programs/tools do as well. If this is the case, it should be deleted right away. It could be a Trojan that spreads viruses and causes data/financial loss as well as other major issues.
How did IDP.Generic infiltrate your computer?
Infections on computers can spread in a variety of ways. Spam campaigns, Trojans, fake/unofficial software updaters, software ‘cracking’ tools. Spam campaigns are used to spread dangerous software by delivering infected attachments in emails.
The majority of the time, their goal is to start a chain reaction.
Unofficial (fake) software updaters cause problems by downloading malicious applications instead of updates/fixes, or by exploiting obsolete software bugs/flaws.
Toolkits for ‘cracking’ software work in a similar way.
They ostensibly get around software activation, but if they spread infections, they download and install dangerous software.
Malicious executables are valid files via untrustworthy software download mechanisms such as Peer-to-Peer networks (torrent clients, eMule, and other similar programs), third-party downloaders, unofficial pages, free file hosting, freeware download portals, and so on.
In conclusion, opening files downloaded through these means can lead to the installation of harmful software.
How to avoid installation of malware?
Only download software from official, reputable websites utilizing direct download links. All of the other channels/tools listed above should be avoided.
It is also critical to keep software up to date; however, only use tools or functions built by official software developers.
Furthermore, do not open email attachments from unknown/suspicious senders. It is unlawful to utilize ‘cracking’ programs (activators) to bypass paid activation, and they frequently result in the download and installation of malware.
Finally, to avoid virus infection, use reliable anti-virus/anti-spyware software. We recommend conducting a scan using Combo Cleaner Antivirus for Windows to detect and remove malware.
Instant automatic malware removal:
Manual threat eradication can be a time-consuming and difficult task that necessitates expert computer abilities.
Combo Cleaner is a professional malware removal solution that is highly recommended for removing malware.
How to remove malware manually?
Manual malware eradication is a difficult operation; it’s usually best to let antivirus or anti-malware solutions handle it for you.
Combo Cleaner Antivirus for Windows is comfortable for removing this infection. If you want to manually remove malware, the first step is to figure out what kind of malware you’re dealing with.
Here’s an example of a potentially dangerous program on a user’s computer:
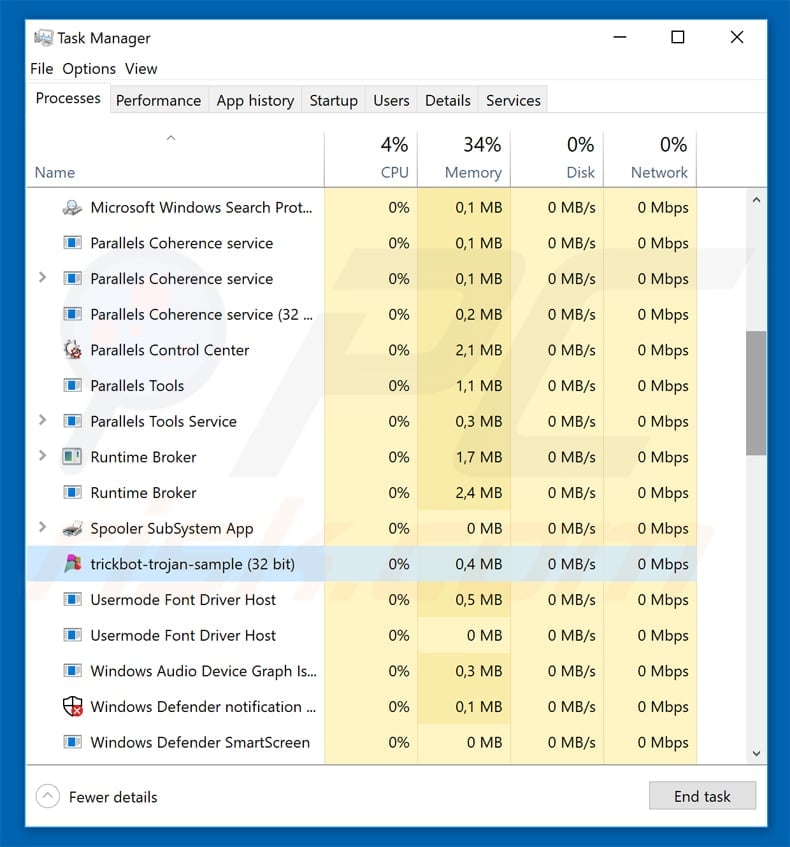
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
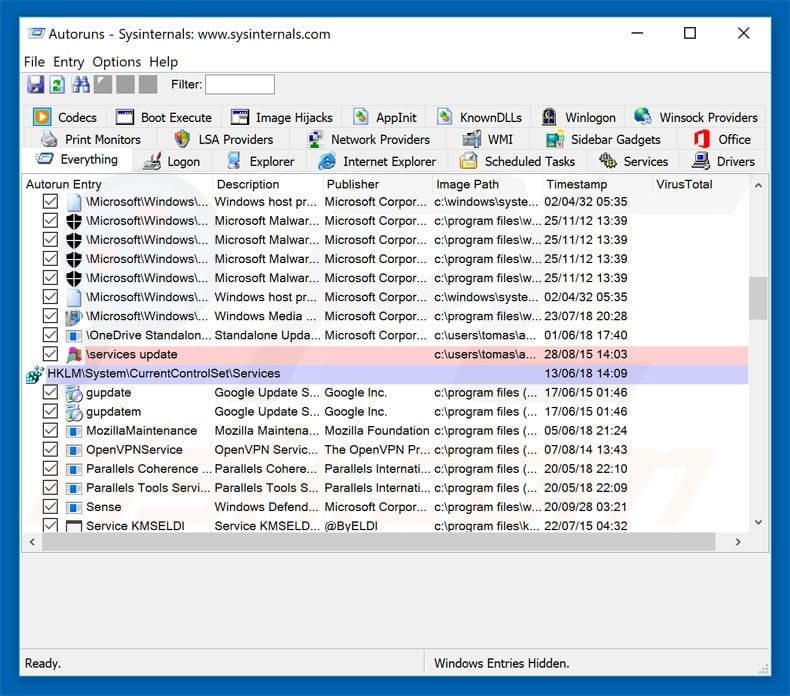
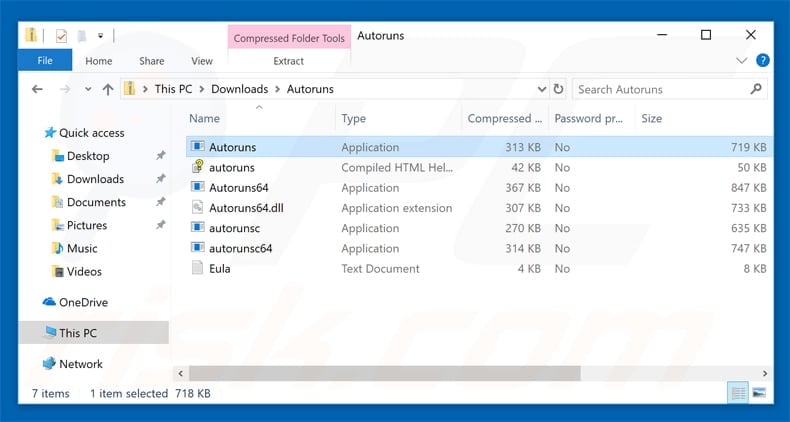
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Start your computer in Safe Mode if you’re using Windows XP or Windows 7.
Click Start, then Shut Down, then Restart, and finally OK. During the startup of your computer, repeatedly press the F8 key on your keyboard until the Windows Advanced Options menu appears, and then pick Safe Mode with Networking from the list.
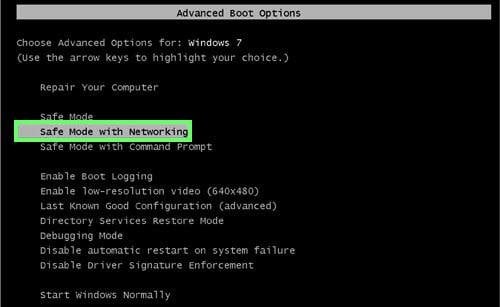
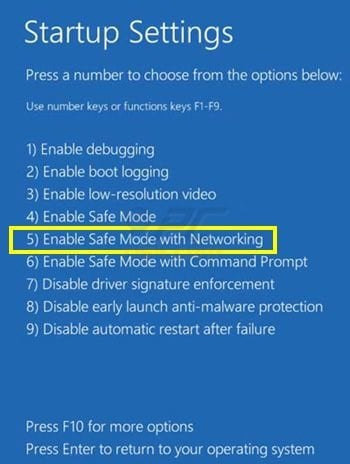
Start for Windows 8 users. Safe Mode with Networking in Windows 8 –
Go to the Windows 8 Start Screen, type Advanced, and then select Settings from the search results.
Select Advanced startup from the “General PC Settings” window that appears when you click Advanced startup choices. Select “Restart now” from the drop-down menu.
The “Advanced Startup settings menu” will now appear when your machine restarts.
Then choose the “Advanced options” button after clicking the “Troubleshoot” button. Click “Startup settings” in the advanced option panel. Select “Restart” from the drop-down menu.
The Startup Settings screen will appear when your computer restarts. To enter Safe Mode with Networking, press F5.
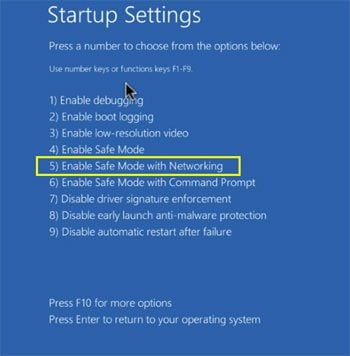
Windows 10 users: Select the Power icon from the Windows logo. While holding the “Shift” key on your keyboard, click “Restart” in the popup menu. Select “Troubleshoot” from the “Pick an option” window, then “Advanced choices.”
Select “Startup Settings” from the advanced options menu and click the “Restart” button.
To open the following window, use the “F5” key on your keyboard. This will reboot your computer in safe mode with networking enabled.
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
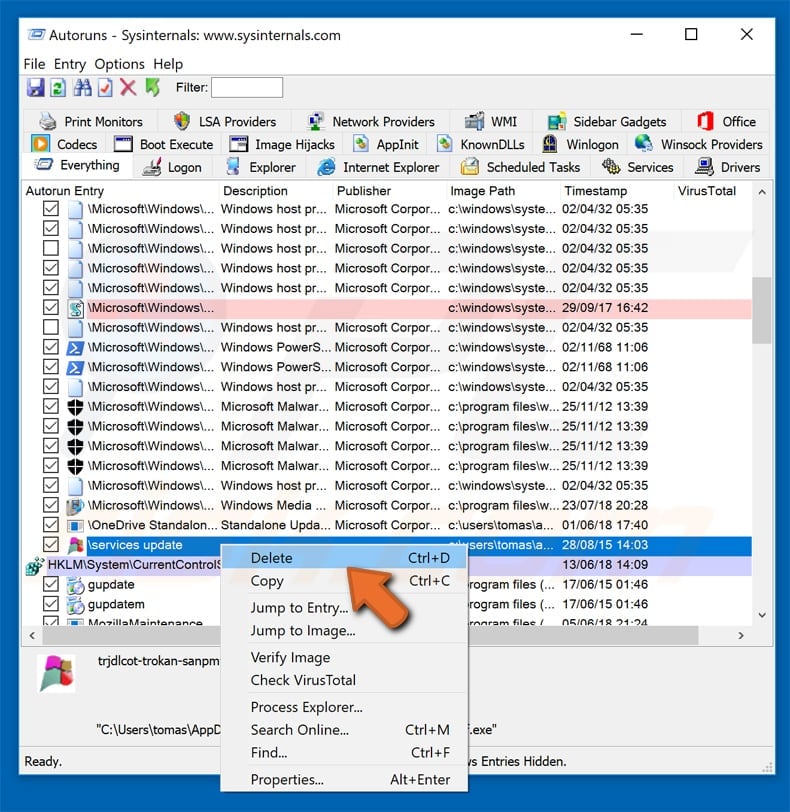
 In the Autoruns application, click “Options” at the top and uncheck the “Hide Empty Locations” and “Hide Windows Entries” options. After this procedure, click the “Refresh” icon.
In the Autoruns application, click “Options” at the top and uncheck the “Hide Empty Locations” and “Hide Windows Entries” options. After this procedure, click the “Refresh” icon.
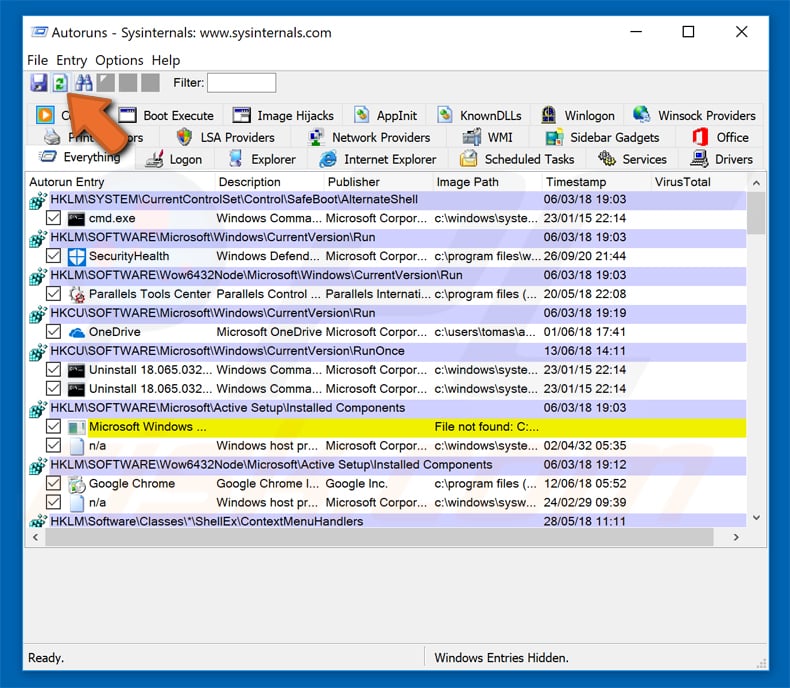
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
That is a good idea to jot down the whole path and name. It’s worth noting that some malware disguises itself as a normal Windows process.
It’s critical to prevent deleting system files at this point. When you’ve found the suspicious software you want to get rid of, right-click on its name and select “Delete.”
You should search for the malware name on your computer after deleting the virus with the Autoruns application (this assures that the malware will not run automatically on the next system startup).
Before continuing, make sure that hidden files and folders are enabled.
If you find the malware’s filename, make sure to delete it.
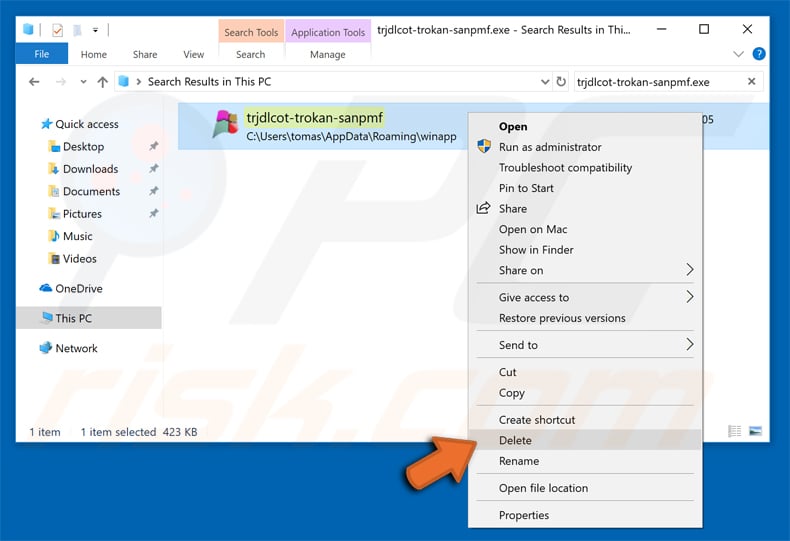
In regular mode, restart your computer.
If you follow these procedures, you should be able to get rid of any virus on your computer.
It’s worth noting that manually removing a threat necessitates significant computer expertise.
Leave malware removal to antivirus and anti-malware tools if you don’t have these talents.
With advanced malware infections, these measures may not be effective.
As always, it is preferable to avoid infection rather than attempt to remove malware later.
Install the most recent operating system updates and utilize antivirus software to keep your computer safe.
We recommend checking your computer using Combo Cleaner Antivirus for Windows to ensure it is free of malware infections.
Click here to read more useful and interesting articles.

